System Vulnerabilities
Is LiquidFiles vulnerable to CVE-YYYY-XXXX?
Please enter the CVE number in the Ubuntu CVE database: https://ubuntu.com/security/cves to see if Ubuntu is vulnerable to a specific CVE number. If/when Ubuntu releases an update, it will be made available to all Ubuntu systems, including LiquidFiles. LiquidFiles v4.x uses Ubuntu 22.04 LTS (Jammy).
Please note that the LiquidFiles version number does not reflect the operating system patch level. If you have enabled automatic system security updates but haven't updated LiquidFiles itself, you may well be running an older version of LiquidFiles and still be fully up to date on system security patches. It's therefore impossible to say exactly what version of a system package like OpenSSH or OpenSSL is installed on your specific LiquidFiles system — it depends on when you installed it and whether you have enabled automatic system security updates.
Regardless if LiquidFiles is currently vulnerable or not, the most important thing you can do is to enable automatic system security updates to stay protected. You can also enable an Ubuntu Pro license for additional security coverage.
Enable Automatic System Security Updates
The most important thing you can do to stay protected long term is to enable automatic system security updates in Admin → System → Updates. This is the default and recommended setting:
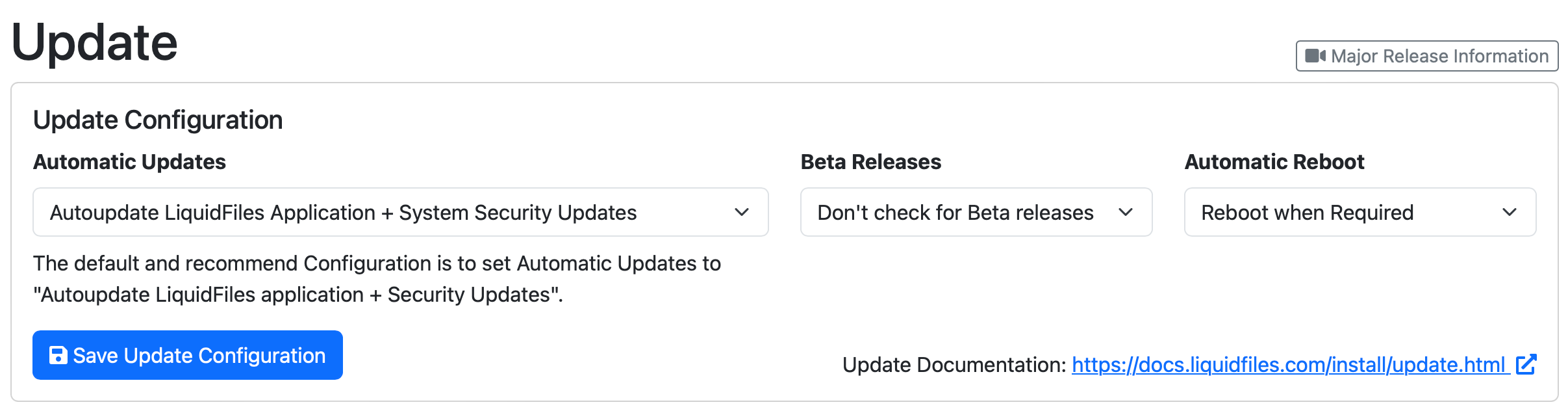
This will ensure that your system is up-to-date with the latest application and security updates and is the safest way to run LiquidFiles. When Ubuntu releases security updates, they will be installed nightly. LiquidFiles application updates will be installed about a week after an update has been released to give extra protection should an issue be detected shortly after release.
Enable an Ubuntu Pro License
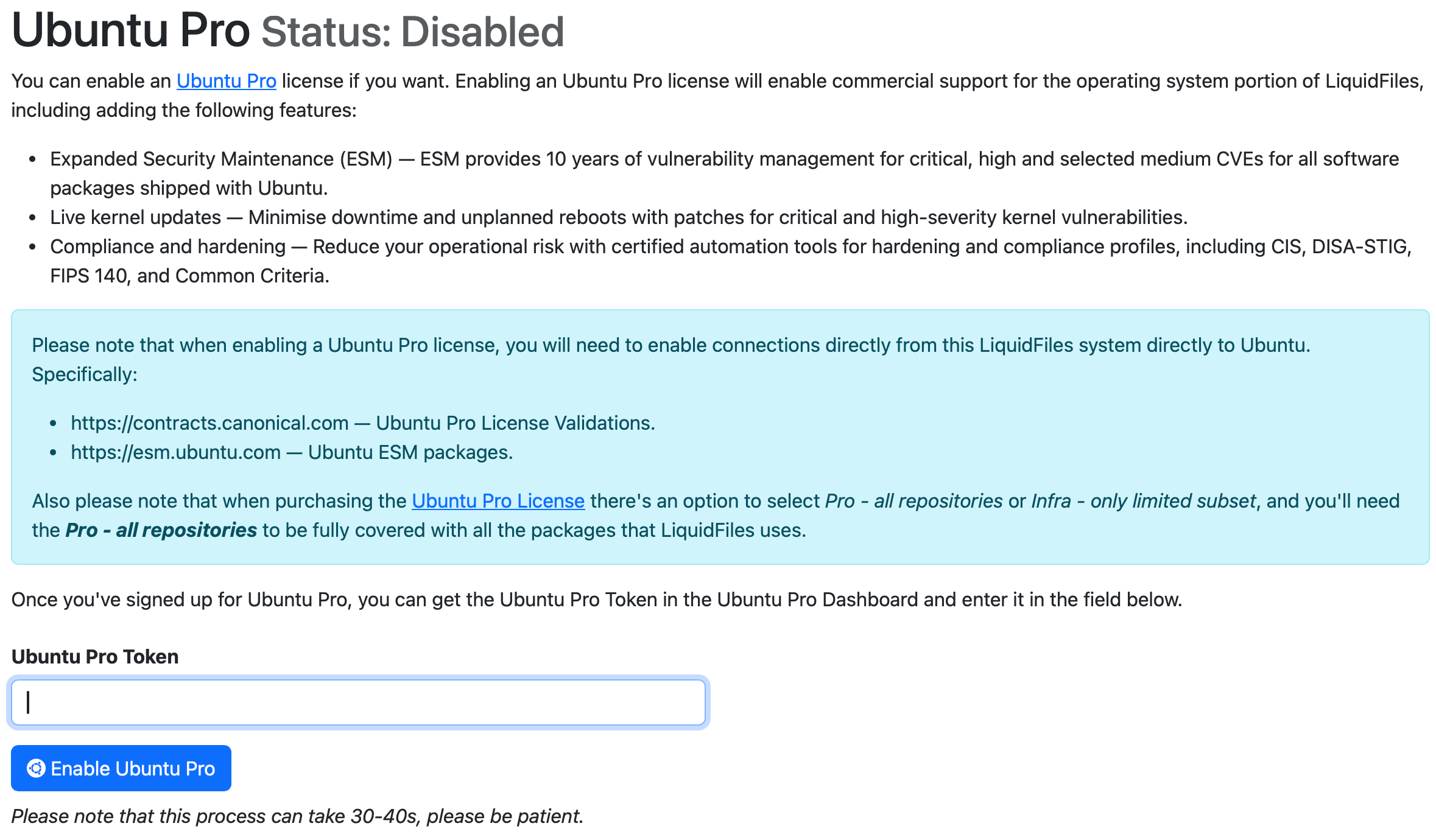
In addition to enabling automatic updates, you can also enable an Ubuntu Pro license in Admin → System → Pro. Ubuntu Pro extends security coverage beyond the standard Ubuntu packages to include additional security patching for thousands of additional packages, as well as compliance tools for certifications such as DISA-STIG, FedRamp, NIST, FIPS 140, HIPAA, PCI and ISO 27001. It also extends Ubuntu LTS support from 5 to 10 years.
Please see the Security Hardening page for more details.
Manual Patching
Every so often we get a question along the lines of "my scanner has reported that the installed OpenSSH version is older than what my scanner thinks it should be, can I just manually install a new version?"
No. If you manually install a version from source, you are almost guaranteed to break the system beyond rescue and the only way forward would be to reinstall LiquidFiles and restore from a backup. All Linux vendors, including Ubuntu (and CentOS that we used in earlier releases) include many operating system specific tweaks to their installations and also manually patch versions without necessarily updating the version to a later release. In other words, an older version may not be vulnerable just because your scanner thinks it is. In order to see if the system is vulnerable, you have to check the CVE database as outlined above, and the most important thing you can do is to enable automatic updates and optionally enable an Ubuntu Pro license as outlined above.
